要約
— alexintosh.eth | I’m hiring23, 2022 Humans can remember in short term memory about six digits with ease for almost everyone, and for the majority they can remember sevendigits, though not with full ease. Few vanity addresses can go seven digits, but plenty wouldn’t be so thorough in checkingeither, withrevoke.cash allowing you to revoke permissions to anycontract, although in this case all the funds may have already been drained. It’s easy to find who asked for that number however, and here the employee is known toNameCheap, and so you lock some up and that should be the end of it because it’s guaranteed jail if you use this method and the funds will be confiscated unless you wantjail-time to go up to lifetime. There’s also other potential solutions like the Ethereum Name Service , though we don’t see that used much for live domain names inproduction, and there’s also BGP hijacks where the ISP redirects tomalicious, but here too law enforcement can find the employee and who done it. That might seem ironic that you now have a centralized gatekeeper telling you what to trust, but you can ignore them if you want and they can’t force you to dosomething, like just change your domain IP as in centralized databases.
本文翻訳
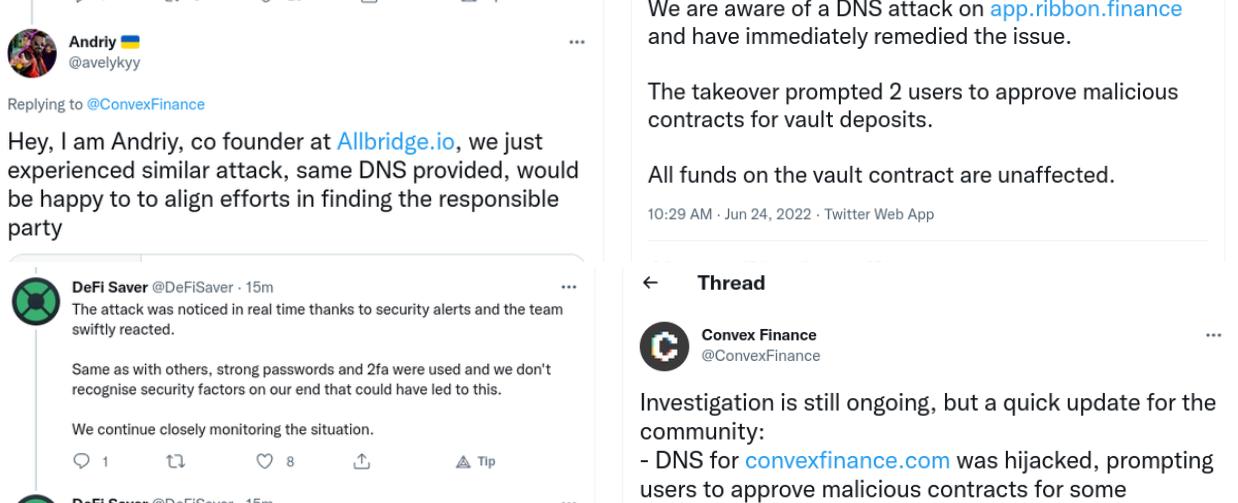
A number of defi dapps, most prominently Convex Finance, had their domain name hijacked. ConvexFinance, Ribbon Finance, DeFiSaver and Allbridge were all affected with users approving malicious contracts while being on the actual domain of the project. The registrar for all these domains was NameCheap, with its CEO, Richard Kirkendall, stating: “We’ve traced this down to a specific Customer Service agent that was either hacked or compromised somehow and have removed all access from this agent. This affected a few targeted domains but we will continue investigating.” Hopefully he or she was also reported to the police and gets jail time because this is a clear and straightforward case of theft with all the evidence presumably available, so it should be a short trial. But the hack or the hijack was clearly not sophisticated at all. Some employee at NameCheap just changed the IP address to which the domain pointed, with all looking identical on the new malicious server, including the first and last four digits of the ethereum address. I don’t what’s happening but be 100% certain you approve exactly 0xF403C135812408BFbE8713b5A23a04b3D48AAE31 if you used @ConvexFinance make sure you did not approve: 0xF403a2c10B0B9feF8f0d4F931df5d86aD187AE31 https://t.co/QTsi6BV1Zj — alexintosh.eth | I’m hiring (@Alexintosh) June 23, 2022 So they’ve used a vanity address, and that too is not sophisticated because you just keep clicking on create new address until you find one that looks similar. This process gets more difficult the more digits you want ‘customized’ by the bot software clicking create new address. Humans can remember in short term memory about six digits with ease for almost everyone, and for the majority they can remember seven digits, though not with full ease. Few vanity addresses can go seven digits, but plenty wouldn’t be so thorough in checking either, with revoke.cash allowing you to revoke permissions to any smart contract, although in this case all the funds may have already been drained. But there’s an employee here and you’d expect NameCheap to fully cooperate or themselves be in trial – criminal trial – so recouping some of the funds should be possible. Because this employee presumably knows for whom they changed the IP, or they get double/triple prison time. So in the end we may have a case of dumb criminals. And according to Kirkendall, the criminal legal system appears to be the only solution here because at least some employees apparently need the ability to change IP in instances where there’s a hack or abuse. For the latter, a better solution may be to cancel the domain or suspend it rather than re-direct. For a hack, maybe there isn’t much of a choice, but this is a dumb crime and so we expect full prosecution and that should be sufficient deterrent. Because there’s no way this activity can be undertaken without it being known who exactly performed the action, with Kirkendall confirming they keep logs of every change and activity. Making this similar to the brief SIM hacking episode where thieves would get someone’s number to use that for two factor authentication. It’s easy to find who asked for that number however, and here the employee is known to NameCheap, and so you lock some up and that should be the end of it because it’s guaranteed jail if you use this method and the funds will be confiscated unless you want jail-time to go up to lifetime. There’s also other potential solutions like the Ethereum Name Service (ENS), though we don’t see that used much for live domain names in production, and there’s also BGP hijacks where the ISP redirects to malicious, but here too law enforcement can find the employee and who done it. So the solution is for these thieves to realize they’re being dumb by our tax money making it very clear through the law enforcement doing the job it is paid for, which most likely they will. While the temporary solution is to be a bit more alert currently, check up to seven digits at least, and if you’ve previously approved, check even more thoroughly. Because they can fake a lot of things, but they can’t fake the actual address, with it unclear whether in the longer term there are also potentially AI solutions where MetaMask or Etherscan warns you. That might seem ironic that you now have a centralized gatekeeper telling you what to trust, but you can ignore them if you want and they can’t force you to do something, like just change your domain IP as in centralized databases.
引用リンク
出典:https://www.trustnodes.com/2022/06/25/defi-dapps-dns-attacked
